Threats Xplorer is specially designed to offer you highly increased visibility over the detected threats in your network. The feature centralizes detection events from multiple GravityZone technologies and classifies them by category, threat type, remediation actions, and many others.
You can easily identify and analyze any event from your company over a specific time interval by using the available filters.
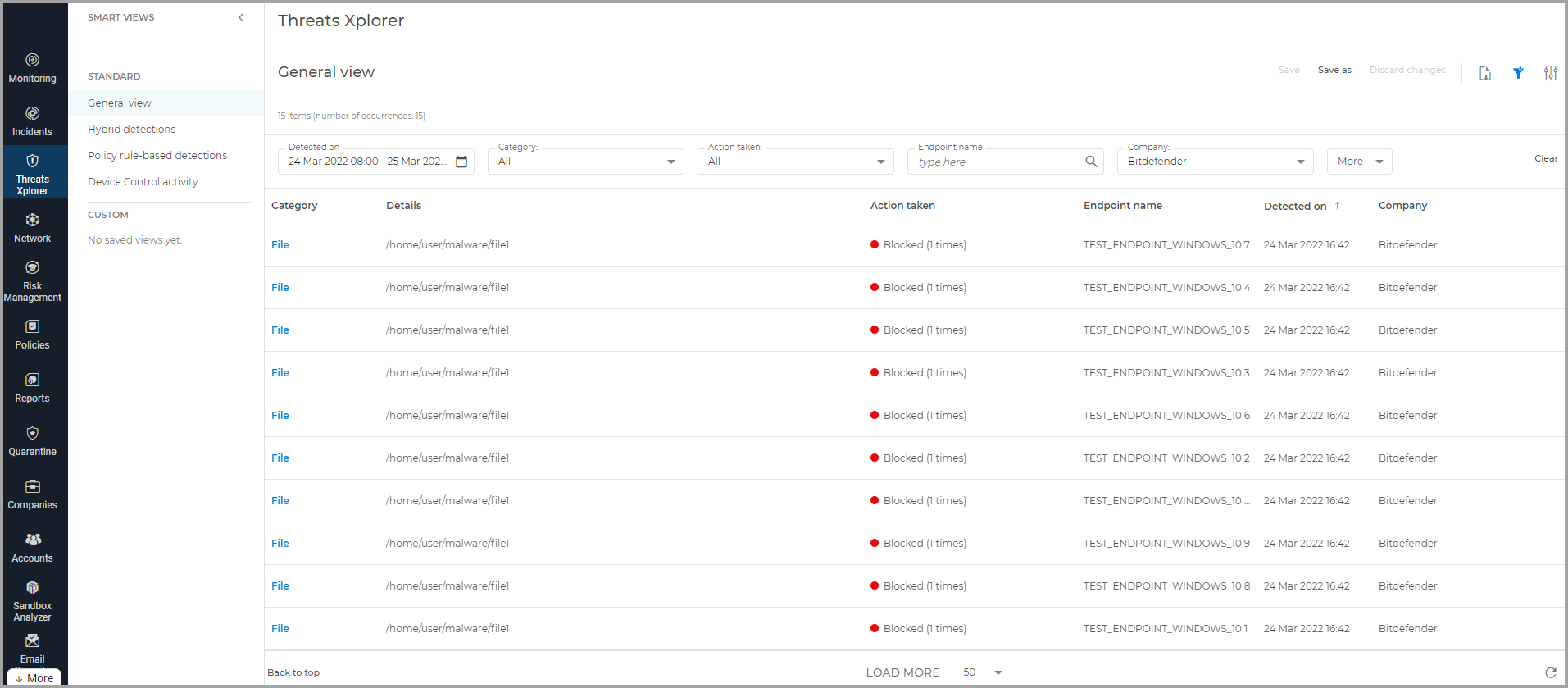
On the Threats Xplorer page, you can view the complete list of the detection events in your network. The grid displays the entries in reverse-chronological order, this way the most recent events are always at the beginning.
Important
The presented data is directly correlated with the selected period, company, and license key.
The grid displays the detection events from the last 90 days.
The feature centralizes detection events from the following modules:
Antimalware
Network Protection
Storage Protection
Exchange Protection
Device Control
Firewall
Page Menu
- Bitdefender – GravityZone
- Viewing notifications
- Executive Summary
- Announcements
- Viewing and managing scheduled reports
- Best practices
- Operation
- Operation
- Configuration
- Reconfigure client
- Reports
- Report types
- Create reports
- Notification types
- Notifications
- Printing reports
- Emailing reports
- Saving reports
- Taking report-based actions
- Configuring notification settings
- Deleting notifications
- Repair client
- Restart machine
- Network discovery
- Changing policy settings
- Configuring profiles
- Assigning policies
- Creating policies
- Troubleshooting
- Patch tasks
- Credentials Manager
- Best practices
- Renaming policies
- Computer policies
- Risk scan
- Update client
- Uninstall client
- Install
- Patch tasks
- Exchange scan
- Deleting policies
- Scan
- Scan for IOC
- Allow file download blocked by Bitdefender
- Features distribution
- Content Control
- Firewall
- Advanced Anti-Exploit
- HyperDetect
- Advanced Threat Control
- Antimalware
- Introduction
- Threats Xplorer
- Network Attack Defense
- Patch Management
- Device Control
- Container Protection
- Security for Storage
- eXtended Detection and Response (XDR)
- Endpoint Risk Analytics (ERA)
- Sandbox Analyzer
- Security for Exchange
- Full Disk Encryption
- Email Security
- Deleting endpoints
- Using Recovery Manager for encrypted volumes
- Assigning policies
- Whitelist Email
- Install security agents – use cases
- Bitdefender Endpoint Security Tools for Linux quick start guide
- AD Connect
- Install Security Server manually
- Install security agents – standard procedure
- Install Security Server through Control Center
- Email Security Licensing & Provisioning
- Configure Email
- Add Mailbox
- Endpoint types
- Creating quick reports
- Running tasks
- Viewing and managing tasks
- Sorting, filtering and searching for endpoints
- Organizing endpoints into Groups
- Viewing endpoint details
- Checking the endpoints status
- Network inventory
- Check my monthly subscription for Bitdefender Security for AWS